With privacy controls under so much scrutiny these days, it’s hardly a surprise when the next scandal comes along. That’s why it’s never been more crucial for companies to adopt a belt-and-braces approach to protect customer data and be clued up about what exactly happens to it.
So, the last thing you’d expect is your security software spying on you, right? ‘Fraid not.
According to analytics company ExtraHop, enterprise security, analytics, and hardware management tools – the nuts and bolts relied on to keep data safe – are busy collecting and sharing information.
Enterprises need to hold their vendors more accountable for how they use their customer data.
Of course, most companies use customer data and, more often than not, probably share it with third parties – a practice entirely above board under their service terms. Enterprises, on the other hand, ExtraHop explains, rely on third-party vendors for everything – infrastructure and applications to security – which can be problematic when they don't know precisely how those vendors are using their data.
ExtraHop discovered the issue after looking at its own customers’ networks and found that, in several instances, their security and analytics software was uploading information to servers outside of the customer’s network without their knowledge or consent.
What data security breaches were found?
‘Phoning home’ data – in other words, exfiltrating data – isn’t necessarily an issue, so long as the customer has been given advance knowledge and approves, and it’s done so securely. But it definitely becomes an issue when customers are unaware that sensitive data is leaving their environment, or that the vendor is even phoning home data in the first place.
...administrators need to monitor their networks to spot anything untoward.
In the report, ExtraHop reveals a mix of products were at it – endpoint security software, a hospital’s device management software, security cameras, and a financial firm’s security analytics software – and all phoning home customers’ data on the quiet, without any knowledge or authorisation.
Without naming names, four real-world examples have been given:
So, while ExtraHop notes that while there may not be any malicious activity in the examples reported, it’s in violation of the law nevertheless. That’s why, it says, administrators need to monitor their networks to spot anything untoward.
It's very difficult for enterprises to really understand what’s happening with their data.
“To be clear, we don’t know why these vendors are phoning home data. The companies are all respected security and IT vendors, and in all likelihood, their phoning home of data was either for a legitimate purpose given their architecture design or the result of a misconfiguration,” the report says.
“But the fact that large volumes of data are travelling outbound from a customer environment to a vendor without the customer’s knowledge or consent is problematic.
“What these examples underscore is that it's very difficult for enterprises to really understand what’s happening with their data. How can you expect to know when a bad actor is exfiltrating data when you don’t know that your trusted vendors are pulling it out of your environment and for what purpose?”
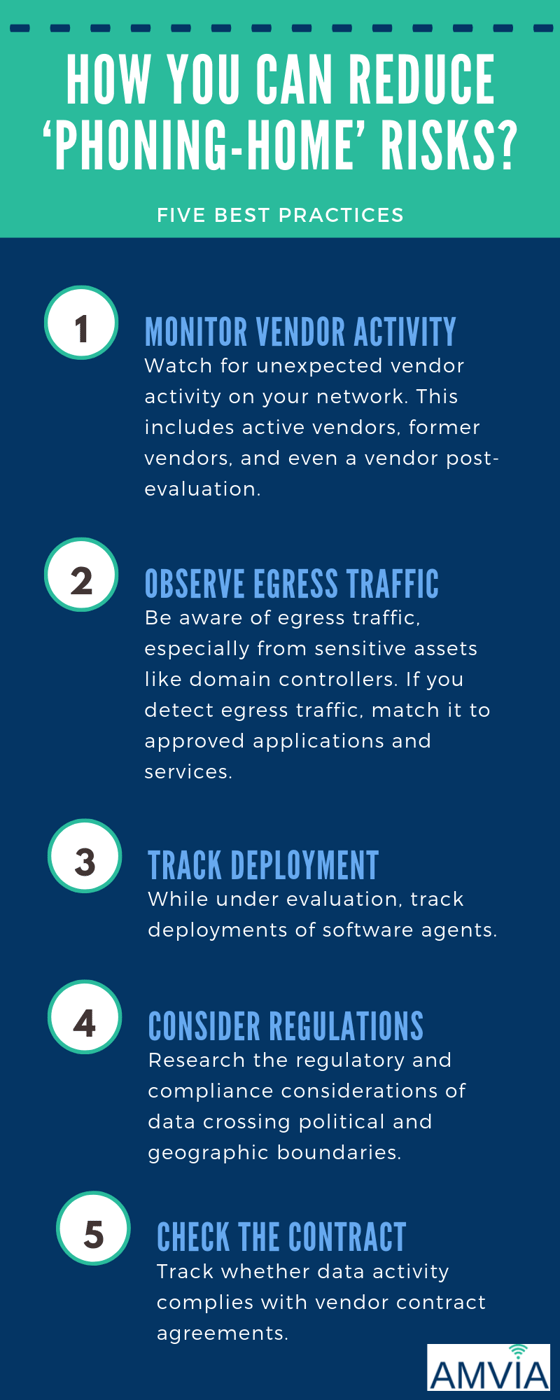
How can companies reduce ‘phoning-home’ risks?
Along with the warning, ExtraHop also gives some useful guidance on reducing these risks and recommends five best practices to improve data security, privacy, and compliance:
ExtraHop’s report is definitely a warning to all enterprises to hold their vendors more accountable for how they use their customer data. On top of these recommendations, ExtraHop also urges companies to question their vendors to make sure they understand how their data is used, where exactly it’s going and what the protocols are for phoning home.
Do this and, ExtraHop says, vendors will be more accountable and – more importantly – limit the vulnerability of sensitive enterprise data.
Further reading: Is Google Listening to Everything You Say?
.png?width=200&height=75&name=Amvia%20New%20Header%20Logo%20(11).png)


.png)